In today's world, every device connected to the Internet has a unique identifier known as an IP address (Internet Protocol address). This address allows devices to interact with each other and serves as the foundation for many network processes, from simple email sending to complex cloud computing systems. Understanding what an IP address is and how it works is key for anyone who wants to use Internet technologies effectively.
The Development History of IP Addresses
IP addressing began with the IPv4 protocol, which was introduced in 1981 and offered more than 4 billion unique addresses. At that time, this seemed sufficient; however, with the expansion of the internet and the increase in the number of connected devices, it became clear that there would not be enough IPv4 addresses for everyone. This led to the development of a new standard — IPv6, which was introduced in the mid-1990s and offered virtually unlimited addresses thanks to 128-bit addressing. The introduction of IPv6 solved the problem of address space exhaustion and opened new opportunities for expanding the global network.
Detailed Explanation of IPv6
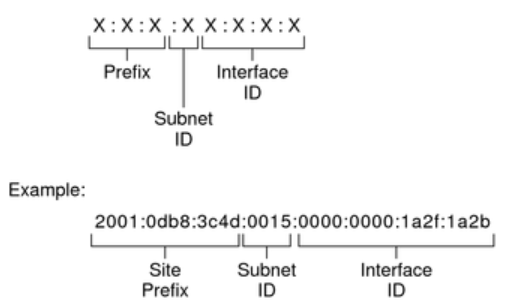
IPv6 expanded the number of available IP addresses and improved routing and security. IPv6 addresses are presented in eight groups of four hexadecimal digits separated by colons, which provides a colossal increase in the number of combinations. For example: 2001:0db8:85a3:0000:0000:8a2e:0370:7334
Advantages of IPv6 include automatic device configuration, improved support for mobile networks, and integration of security at the protocol level, making networks more secure against various types of attacks. For example, IPv6 includes mandatory support for IPsec, which provides encryption and authentication at the IP packet level.
Technical Details of IP Addresses
IP addresses play a key role in data routing within a network, allowing information to find the correct path from source to recipient. Each packet of data sent over the internet contains the IP address of the sender and the recipient. Network devices, such as routers, use these addresses to determine the best path for data transmission. Efficient routing ensures not only the fast delivery of data but also enhances the reliability and efficiency of network connections.
Security Issues Associated with IP Addresses
IP addresses can be a potential point of vulnerability in network security. Since an IP address can be used to determine the location of a device and other related information, it can become a target for cyberattacks such as port scanning, DDoS attacks, and fraud. To protect against such threats, it is important to use modern methods of ensuring confidentiality, including encrypting traffic and using anonymous services such as VPNs and proxy servers.
Furthermore, for security at the network level, it is recommended to regularly conduct audits and updates to prevent vulnerabilities and protect sensitive data.
Filtering IP addresses using firewalls and access control lists (ACLs) is also an important practice that allows controlling access to network resources based on the source or destination address.
Practical Use of IP Addresses
IP addresses find diverse applications in the daily activities of both ordinary users and large organizations:
- Web Hosting: Static IP addresses are typically used to host web servers, which must be constantly available on the internet.
- Internet of Things (IoT): IoT devices, such as smart home appliances, sensors, and surveillance cameras, often have their own IP addresses for exchanging data over the internet.
- Cloud Computing: IP addressing is critical for accessing remote cloud resources and services, such as data storage, virtual machines, and applications.
For ordinary users, dynamic IP addresses offer convenience and security, as their IP address changes with each internet connection, making it difficult to track their activities. Companies can use IP address management to control network traffic, allocate resources, and ensure the security of their networks.
Distribution and Assignment of IP Addresses
IP addresses are distributed and managed globally by the IANA (Internet Assigned Numbers Authority). IANA allocates blocks of IP addresses to regional internet registries (RIRs), which in turn distribute them to internet providers and organizations in their regions.
Internet providers typically assign static public IP addresses to servers and dynamic private IP addresses to home users through the DHCP protocol.
Compatibility Mechanisms between IPv4 and IPv6
To ensure a smooth transition from IPv4 to IPv6, special compatibility mechanisms have been developed:
- Dual Stack: Allows devices to support both protocols (IPv4 and IPv6) simultaneously for backward compatibility.
- Tunneling: Encapsulates IPv6 packets in IPv4 packets (or vice versa) to transmit traffic across networks with a different protocol version.
- Address Translation (NAT64, DNS64): Converts addresses and names between IPv4 and IPv6 to ensure interaction.
The Future of IP Addresses
With the increasing number of devices connected to the Internet and the development of technologies such as the Internet of Things (IoT), the need for IP addresses continues to grow. This stimulates the further spread of IPv6, as it allows addressing virtually an unlimited number of devices. In the future, we can expect new improvements in IP address management and routing to cope with the increasing volume of data and heightened security requirements. Additionally, the development of artificial intelligence and machine learning may lead to the creation of smarter networks, which can automatically optimize their operation and address management in real-time.
Glossary of Terms:
- IANA - Internet Assigned Numbers Authority: The organization responsible for distributing IP addresses.
- RIR - Regional Internet Registry:
- DHCP - Dynamic Host Configuration Protocol: A protocol for automatically assigning IP addresses.
- IPsec - A protocol that provides encryption of IP traffic.
- ACL - Access Control List: A list for filtering IP addresses.
- VPN - Virtual Private Network: A private network for access through an encrypted connection.